Each year, the Institute for Cyber Security, in collaboration with the IT Support Services, hosts Cyber Security Day. This daylong event features nationally recognized security experts as well as speakers from law enforcement, government, security industry, and academia. Cyber Security Day is open to the public, community colleges, and neighboring universities.
The thirteenth annual Cyber Security Day was held Tuesday, October 20, 2020, live via Zoom.
Information for the Event
The thirteenth annual Cyber Security Day featured presentations from James Joshi, Isaac Porche, Jack Lange, and Murat Ozturan, and a panel discussion with Amy Diehl, Tom Dugas, and Paul Grieggs. Topics included privacy, cyber attack life cycles, digital rights, digital resilience, and many others. Download the 2020 document packet to view the flyer, brochure, and schedule. Visit the Photo Gallery to see event photos.
Guest Speaker Biographical Information
Dr. James Joshi, Professor and Director of LERSAIS, School of Computing and Information, the University of Pittsburgh
 James Joshi is a professor of School of Computing and Information at the University of Pittsburgh, and the director/founder of the Laboratory of Education and Research on Security Assured Information Systems (LERSAIS). He is currently serving as an NSF program director in the Computer and Network System division and in the Secure and Trustworthy Cyberspace program. He is an elected Fellow of the Society of Information Reuse and Integration, a senior member of the IEEE, and a distinguished member of the ACM. His research interests include access control models, security and privacy of distributed systems, trust management, and secure and privacy-preserving Machine Learning. He is a recipient of the NSF CAREER award in 2006. He established and managed the NSF CyberCorp Scholarship for Service program at Pitt in 2006 (two rounds). He also established LERSAIS as a NSA-designated Center of Academic Excellence in Cyber Defense (both CAE and CAE-R) and has been managing it.
James Joshi is a professor of School of Computing and Information at the University of Pittsburgh, and the director/founder of the Laboratory of Education and Research on Security Assured Information Systems (LERSAIS). He is currently serving as an NSF program director in the Computer and Network System division and in the Secure and Trustworthy Cyberspace program. He is an elected Fellow of the Society of Information Reuse and Integration, a senior member of the IEEE, and a distinguished member of the ACM. His research interests include access control models, security and privacy of distributed systems, trust management, and secure and privacy-preserving Machine Learning. He is a recipient of the NSF CAREER award in 2006. He established and managed the NSF CyberCorp Scholarship for Service program at Pitt in 2006 (two rounds). He also established LERSAIS as a NSA-designated Center of Academic Excellence in Cyber Defense (both CAE and CAE-R) and has been managing it.
Dr. Isaac Porche, Deputy Director of the Applied Research Lab at Penn State University
 Isaac Porche received his PhD in electrical engineering and computer science from the University of Michigan. He currently heads the Communications, Information, and Navigation Office at Penn State's Applied Research Lab. Most recently, Porche was a research scientist and chief engineer at General Dynamics Mission Systems. Previously, he worked as a senior engineer at the RAND Corporation and program director for the Homeland Security Operational Analysis Center. He also served as associate director of the RAND Arroyo Center's Forces and Logistics Program. His areas of expertise include acquisition, homeland security, cybersecurity network and communication technology, intelligence, surveillance, reconnaissance, information assurance, big data, and cloud computing. He has led research projects for the US Navy, US Army, the Department of Homeland Security, the Joint Staff, and the Office of the Secretary of Defense.
Isaac Porche received his PhD in electrical engineering and computer science from the University of Michigan. He currently heads the Communications, Information, and Navigation Office at Penn State's Applied Research Lab. Most recently, Porche was a research scientist and chief engineer at General Dynamics Mission Systems. Previously, he worked as a senior engineer at the RAND Corporation and program director for the Homeland Security Operational Analysis Center. He also served as associate director of the RAND Arroyo Center's Forces and Logistics Program. His areas of expertise include acquisition, homeland security, cybersecurity network and communication technology, intelligence, surveillance, reconnaissance, information assurance, big data, and cloud computing. He has led research projects for the US Navy, US Army, the Department of Homeland Security, the Joint Staff, and the Office of the Secretary of Defense.
Dr. Jack Lange, Associate Professor of Computer Science at the University of Pittsburgh
 Before joining the Department of Computer Science at the University of Pittsburgh in the fall of 2010, John "Jack" Lange received his PhD and MS degrees in computer science from Northwestern University (2006 and 2010). Prior to that he received a BS in computer engineering as well as a BS in computer science, also from Northwestern University (2003). Over the past 15 years his work has focused on high performance computing and operating systems, as well as networking, virtualization, and distributed systems. More recently he has begun conducting research into practical system architectures to ensure user-oriented security and privacy. Currently he is working on leveraging hardware support to allow users to retain control of personal data in the era of cloud computing and social media services.
Before joining the Department of Computer Science at the University of Pittsburgh in the fall of 2010, John "Jack" Lange received his PhD and MS degrees in computer science from Northwestern University (2006 and 2010). Prior to that he received a BS in computer engineering as well as a BS in computer science, also from Northwestern University (2003). Over the past 15 years his work has focused on high performance computing and operating systems, as well as networking, virtualization, and distributed systems. More recently he has begun conducting research into practical system architectures to ensure user-oriented security and privacy. Currently he is working on leveraging hardware support to allow users to retain control of personal data in the era of cloud computing and social media services.
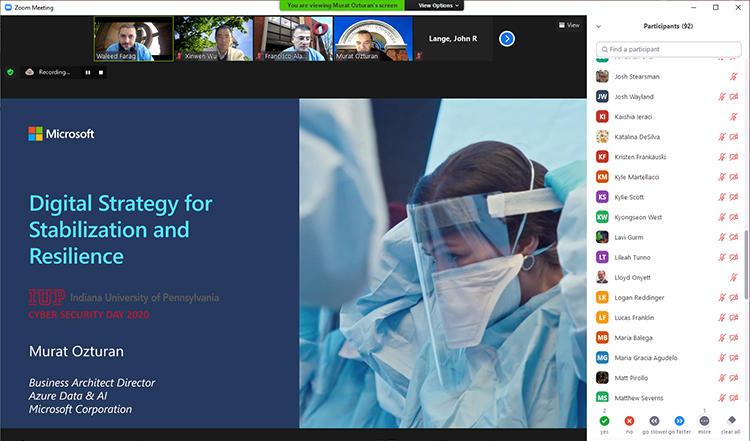
Mr. Murat Ozturan, Business Architect Director, Azure Data & AI at Microsoft Corporation
 Murat Ozturan is a proud graduate of IUP in 1990 with a computer science degree.He is business architect director in the Customer Success Unit responsible for Azure Data&AI. He is accountable for driving business and technology strategy for Data&AI solutions architecture and engineering in worldwide commercial business; working closely with key stakeholders across engineering, marketing, and field organizations; and driving customer success for cloud implementations.Previously, he was an Azure Data engineering member responsible for driving all technology initiatives, tools, and customer services for migrating data-related solutions/products from existing and competitive platforms to modern data platforms. He was also responsible for building OSSDB (PostgreSQL, MySQL, MariaDB) partner ecosystem. He was the CTO of Asia, Pacific, and Japan for Services until 2016, based out of Singapore, responsible for setting the technical strategy in services across Asia. He is a Microsoft veteran who is one of the North Africa/Turkey region's founding members. He has substantial field experience from TS to practice manager, resulting in a claim to perform all possible technical roles in a field organization successfully.Before Microsoft, Murat worked for Renault-France (automotive), and a major bank in Turkey. For more details: Murat Ozturan.
Murat Ozturan is a proud graduate of IUP in 1990 with a computer science degree.He is business architect director in the Customer Success Unit responsible for Azure Data&AI. He is accountable for driving business and technology strategy for Data&AI solutions architecture and engineering in worldwide commercial business; working closely with key stakeholders across engineering, marketing, and field organizations; and driving customer success for cloud implementations.Previously, he was an Azure Data engineering member responsible for driving all technology initiatives, tools, and customer services for migrating data-related solutions/products from existing and competitive platforms to modern data platforms. He was also responsible for building OSSDB (PostgreSQL, MySQL, MariaDB) partner ecosystem. He was the CTO of Asia, Pacific, and Japan for Services until 2016, based out of Singapore, responsible for setting the technical strategy in services across Asia. He is a Microsoft veteran who is one of the North Africa/Turkey region's founding members. He has substantial field experience from TS to practice manager, resulting in a claim to perform all possible technical roles in a field organization successfully.Before Microsoft, Murat worked for Renault-France (automotive), and a major bank in Turkey. For more details: Murat Ozturan.
Dr. Amy Diehl, Associate Vice President and Chief Information Technology Officer, Shippensburg University of Pennsylvania
 Amy Diehl received her PhD in 2013 in administration and leadership studies from IUP. She also has bachelor's degrees in computer science and French from Shippensburg University as well as an MBA from Frostburg State University. Amy has worked in higher education information technology for the past 25 years, currently serving as associate vice president and chief information technology officer at Shippensburg University. Cybersecurity has been part of her portfolio since the beginning of her career; not just from a technical perspective, but also including security policy, safeguarding processes, and risk assessment. She leads the university through the creation of a comprehensive annual information security plan, and she developed the university's employee information security education program. Amy is also a regular speaker at conferences on challenges experienced by women leaders as well as a guest lecturer and consultant on gender bias. She was recognized in 2019 by theCentral Penn Business Journalas a Woman of Influence.
Amy Diehl received her PhD in 2013 in administration and leadership studies from IUP. She also has bachelor's degrees in computer science and French from Shippensburg University as well as an MBA from Frostburg State University. Amy has worked in higher education information technology for the past 25 years, currently serving as associate vice president and chief information technology officer at Shippensburg University. Cybersecurity has been part of her portfolio since the beginning of her career; not just from a technical perspective, but also including security policy, safeguarding processes, and risk assessment. She leads the university through the creation of a comprehensive annual information security plan, and she developed the university's employee information security education program. Amy is also a regular speaker at conferences on challenges experienced by women leaders as well as a guest lecturer and consultant on gender bias. She was recognized in 2019 by theCentral Penn Business Journalas a Woman of Influence.
Mr. Tom Dugas, Assistant Vice President and Chief Information Security Officer for Duquesne University
 Tom Dugas is responsible for leading the information (cyber) security program to protect the availability, confidentiality, and integrity of data and systems at Duquesne University. Tom is a certified information systems security professional and is a graduate of Robert Morris University with a master's degree in communication and information systems and a bachelor's degree in business administration with majors in accounting and management information systems. In 2019, Tom was recognized as the CISO of the Year by the Pittsburgh Technology Council. Tom serves as a leader within the region as a co-leader of the Greater Pittsburgh CISO Group, a member of the Advisory Board for the Pittsburgh CIO Forum, and part of the Governing Body of the Pittsburgh CIO Executive Summit.
Tom Dugas is responsible for leading the information (cyber) security program to protect the availability, confidentiality, and integrity of data and systems at Duquesne University. Tom is a certified information systems security professional and is a graduate of Robert Morris University with a master's degree in communication and information systems and a bachelor's degree in business administration with majors in accounting and management information systems. In 2019, Tom was recognized as the CISO of the Year by the Pittsburgh Technology Council. Tom serves as a leader within the region as a co-leader of the Greater Pittsburgh CISO Group, a member of the Advisory Board for the Pittsburgh CIO Forum, and part of the Governing Body of the Pittsburgh CIO Executive Summit.
Mr. Paul Grieggs, Executive Director of IT Security at Indiana University of Pennsylvania
 Paul Grieggs is responsible for IT security, networking, and systems architecture at IUP. Paul has over 30 years of IT experience. He was the founding director of IUP's IT Security Office in 2015. Prior to his current position, he served as Technical Services manager at IUP and was responsible for networks, central systems, telecommunications, and IT security. Before joining IUP, he served as a technical consultant specializing in communication systems in the banking and health insurance industries. Paul was selected as a finalist for Pittsburgh Technology Council's Chief Information Security Officer of the Year award in 2019. Paul holds a BBA degree from St. Bonaventure University.
Paul Grieggs is responsible for IT security, networking, and systems architecture at IUP. Paul has over 30 years of IT experience. He was the founding director of IUP's IT Security Office in 2015. Prior to his current position, he served as Technical Services manager at IUP and was responsible for networks, central systems, telecommunications, and IT security. Before joining IUP, he served as a technical consultant specializing in communication systems in the banking and health insurance industries. Paul was selected as a finalist for Pittsburgh Technology Council's Chief Information Security Officer of the Year award in 2019. Paul holds a BBA degree from St. Bonaventure University.
Titles and Abstracts
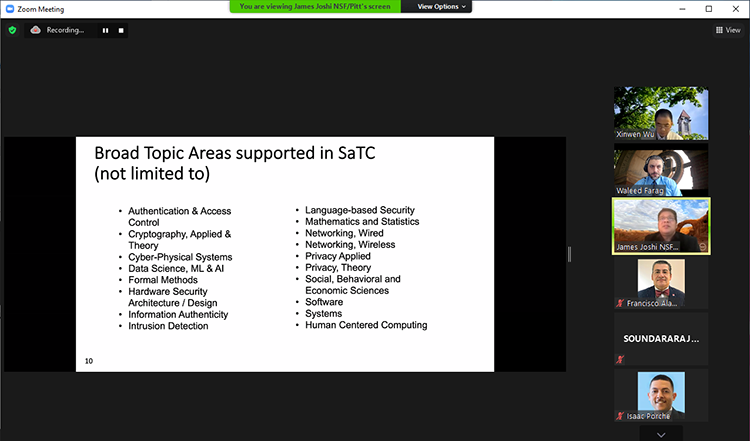
James Joshi, Professor and Director of LERSAIS, School of Computing and Information, the University of Pittsburgh
- Title: Cybersecurity and Privacy: Challenges Ahead
- Abstract:The world has become an intricately interconnected, complex system spanning cyber, physical, human and social elements. As rapid growth in technological innovations continue to present us with unprecedented opportunities for social and economic transformations, these very innovative tools also pose increasing risks to the well-being and safety of individuals and our global society, including during crisis situations such as the current pandemic. To ensure maximal benefits of the cyber enabled world and minimize such risks, it is important to understand holistically the cybersecurity and privacy issues the current and emerging IT innovations introduce so as to tackle them effectively. In this talk, I will discuss the cybersecurity and privacy challenges, as well as resilience issues, and priorities in our current and emerging cyberspace.
Isaac Porche, Deputy Director of the Applied Research Lab at Penn State University
- Title: Cyber Attack Life Cycles
- Abstract: Attacks in cyberspace are deliberate and usually follow patterns. Often, attacks are long-lasting campaigns. Thus, a firm understanding of the steps and phases of an attack allows a higher probability of a defender detecting and mitigating it. This talk outlines common steps seen for such offensive cyber operations. Specifically, this talk provides examples and case studies to illustrate the steps involved in data exfiltration, attacks on industrial control systems, and general denial of service (DOS) attacks using large botnets.
Jack Lange, Associate Professor of Computer Science at the University of Pittsburgh
- Title: Digital Rights Management for the Masses
- Abstract: Cloud-based data sharing services are a mainstay of modern cloud service architectures, but in recent years have suffered a significant amount of loss in confidence among the general public. Numerous cases have come to light where service providers have accessed user data in ways that users find unacceptable, disclosed data to 3rd parties that users were unaware of and did not approve, and lost control of the data itself due to attacks or unintentional data leaks. Recently our research group has explored the use of hardware-based security features available in modern commodity processors, to allow users to retain control over their data even after sharing it in the cloud. While these hardware features were originally intended to restrict how users accessed data from content providers, our work inverts their use to restrict how cloud service providers are able to access the data of their end users. As part of our work we are exploring sustainable data sharing architectures that allow monetization of user data, without requiring users to completely give up control over how their data is used.
Murat Ozturan,Business Architect Director, Azure Data and AI at Microsoft Corporation
- Title: Building Digital Resilience
- Abstract:Almost overnight the world has changed. #FlatteningTheCurve and other measures have led to remote work, productivity shifts, and severe business disruption.Organizations rely upon partners, planning, and often heroics; we are all doing the best we can. It's incumbent upon us to learn, grow, and become stronger during these times. Our businesses, interactions, and approaches will also change as we conquer the pandemic and embrace our learnings.Some businesses will not recover post-COVID-19. Others may shift focus, change operating models, and might even seek to acquire undervalued companies. Whether customer interactions, continuity, contingency planning, or operations, change is certain.The future is bright to learn and innovate if we embrace a growth mindset and lead.
Panel Discussion: Amy Diehl, Tom Dugas, and Paul Grieggs
- Panel Title: So You Want to Work in Cybersecurity?
- Abstract: Demand is very high for new workers to enter various career paths related to cyber security, and there is no end in sight to this rapid growth. But there are so many specialty areas and industry sectors that lifelong learning choices based upon employee interests and skill sets create a path that remains unclear. To top it off, cyber security remains a quickly evolving career field and must draw from individuals from all types of backgrounds to meet demand. All of this can add up to a lot of doubt for newcomers to the field.
This panel features highly accomplished higher education information technology leaders from our region, providing a mix of their perspectives on what students attempting to embark on a career in cyber security may want to consider. Faculty helping to educate and guide students and IT professionals looking for insight from IT leaders should also benefit from the dialogue.
More Information
For more information about Cyber Security Day at IUP, please contact Waleed Farag, director, Institute for Cybersecurity, at farag@iup.edu, 724-357-7995.